Conversation
 jparsons04
left a comment
jparsons04
left a comment
There was a problem hiding this comment.
Some nitty things and other external considerations to think about.
README.md
Outdated
|
|
||
| When you have multiple services in a Layer0 environment, how do you get them to connect to each other? One simple answer is that you hardcode service endpoints (i.e. a Loadbalancer URL) in your application configurations. That may be OK for testing, but ultimately hardcoding endpoints is not portable, annoying to maintain, and not in line with the [guidelines of a 12-factor app](https://12factor.net/). A much better solution is to use a service like Consul, which along with another tool called Registrator, can automatically detect your services when they come online and add them to a service registry. You can then 'discover' these services using catalog endpoints via [DNS](https://www.consul.io/docs/agent/dns.html) or [HTTP](https://www.consul.io/docs/agent/http.html). | ||
|
|
||
| For a practical applications of Consul, see our [Layer0 Consul Documentation](http://docs.xfra.ims.io/guides/consul/). |
There was a problem hiding this comment.
[sort of nit] This sentence doesn't make sense grammatically and the link is now out of date.
There was a problem hiding this comment.
True. Docs are still WIP, I'll get to those tmrw.
| environment_id = "${layer0_environment.consul.id}" | ||
| } | ||
|
|
||
| resource "layer0_environment" "consul" { |
There was a problem hiding this comment.
Just want to make a future note that adding the consul environment in this module will likely have implications for the layer0 walkthroughs that consume this module (for instance, if the walkthroughs have terraform files that make their own consul environment)
There was a problem hiding this comment.
This environment is created by the HelloWorld application, I kept the Consul module behavior (of not creating an environment by itself) as-is.
| name = "consul" | ||
| // TODO: Remove hardcoded AMI | ||
| ami = "ami-f5fc2c8d" | ||
| min_count = 3 |
There was a problem hiding this comment.
in the future, would be nice to have min_count determined internally by scheduler...
i consider it dangerous that users need to manually set this based on sum of discrete ECS instances that will end up getting spun up.
There was a problem hiding this comment.
I agree this is not ideal, and we're talking about ways to make it less dangerous within our current Layer0 refactor. That being said, there is an argument for the explicitness here and how such apps are not designed to run on Layer0 in the first place.
| { | ||
| "name": "consul-agent", | ||
| "image": "consul:${consul_version}", | ||
| "privileged": true, |
There was a problem hiding this comment.
i see the port 53 binding on the Server template, not not the Agent. is the Server the only one that actually needs this?
There was a problem hiding this comment.
It makes things a lot easier for the Server specifically because dealing w the Docker bridge IP is a pain. As for the Agent, technically containers local to it can use the Agent's exposed dns port for resolution as well. As such, I considered having the Agent follow the same port mapping pattern as Server but I opted not to in order to keep changes to a minimum. Could be convinced otherwise, though...
There was a problem hiding this comment.
well this does make sense if you are using the Agent specifically for DNS service discovery... so yeah... i'll buy that... but an example of that in your getting started would be cool
| { | ||
| "name": "registrator", | ||
| "image": "gliderlabs/registrator:latest", | ||
| "privileged": true, |
There was a problem hiding this comment.
why does registrator also need to be privileged?
There was a problem hiding this comment.
because it already requires mounting the docker socket http://gliderlabs.github.io/registrator/latest/ (see their runtime params), which is effectively privileged behavior anyway. I prefer making this overall behavior more explicit.
| environment = "${var.environment_id}" | ||
| deploy = "${layer0_deploy.consul.id}" | ||
| load_balancer = "${layer0_load_balancer.consul.id}" | ||
| size = "t2.medium" // https://www.consul.io/docs/guides/performance.html#minimum-server-requirements |
There was a problem hiding this comment.
FYI i don't think size works for previous (<=0.10.3) versions of L0
This PR updates Consul to use the latest 1.0.1 version, which introduced several new pieces of functionality and/or breaking changes. Several runtime configuration options for Consul needed to be changed as a result, with some new features added as well.
Details
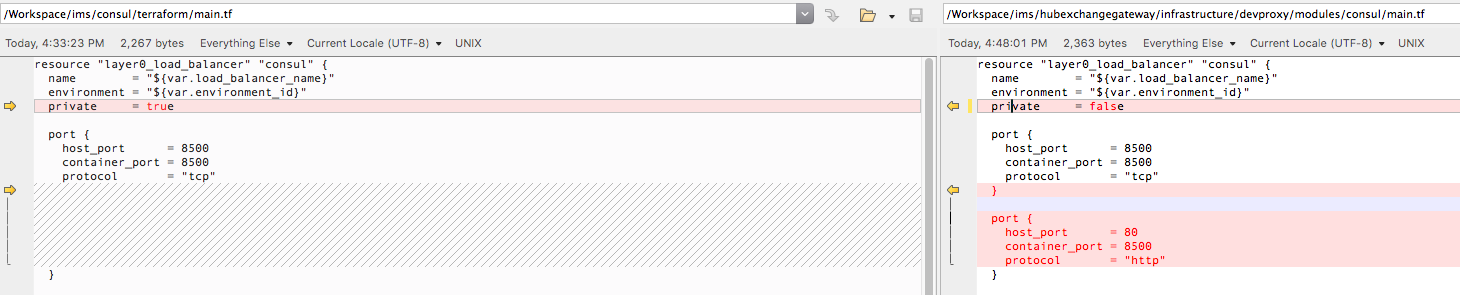
aws-retry-joinfunctionality, which can target a tagged cluster for new node joins. This is an improvement over using an ELB for bootstrapping a Consul cluster.hostnetworking for Consul server containers, and configured DNS to listen on port 53 rather than an overly complex port mapping from 8600 as we had previously.devenvironment and Consul into two separate environments withlinkenabled.min_countfor Consul's environment to ensure that server instances are not scaled downTesting
Extensive manual testing on Layer0 v0.10.3; will need future testing on v0.11.0.
TODO