News: still worry about how to write the correct Casbin policy? Casbin online editor is coming to help! Try it at: http://casbin.org/editor/
Casbin is a powerful and efficient open-source access control library for Golang projects. It provides support for enforcing authorization based on various access control models.
 |
 |
 |
 |
|---|---|---|---|
| Casbin | jCasbin | node-Casbin | PHP-Casbin |
| production-ready | production-ready | production-ready | production-ready |
 |
 |
 |
 |
|---|---|---|---|
| PyCasbin | Casbin4D | Casbin-Net | Casbin-RS |
| production-ready | experimental | WIP | WIP |
- Supported models
- How it works?
- Features
- Installation
- Documentation
- Online editor
- Tutorials
- Get started
- Policy management
- Policy persistence
- Policy consistence between multiple nodes
- Role manager
- Multi-threading
- Benchmarks
- Examples
- How to use Casbin as a service?
- Our adopters
- ACL (Access Control List)
- ACL with superuser
- ACL without users: especially useful for systems that don't have authentication or user log-ins.
- ACL without resources: some scenarios may target for a type of resources instead of an individual resource by using permissions like
write-article,read-log. It doesn't control the access to a specific article or log. - RBAC (Role-Based Access Control)
- RBAC with resource roles: both users and resources can have roles (or groups) at the same time.
- RBAC with domains/tenants: users can have different role sets for different domains/tenants.
- ABAC (Attribute-Based Access Control): syntax sugar like
resource.Ownercan be used to get the attribute for a resource. - RESTful: supports paths like
/res/*,/res/:idand HTTP methods likeGET,POST,PUT,DELETE. - Deny-override: both allow and deny authorizations are supported, deny overrides the allow.
- Priority: the policy rules can be prioritized like firewall rules.
In Casbin, an access control model is abstracted into a CONF file based on the PERM metamodel (Policy, Effect, Request, Matchers). So switching or upgrading the authorization mechanism for a project is just as simple as modifying a configuration. You can customize your own access control model by combining the available models. For example, you can get RBAC roles and ABAC attributes together inside one model and share one set of policy rules.
The most basic and simplest model in Casbin is ACL. ACL's model CONF is:
# Request definition
[request_definition]
r = sub, obj, act
# Policy definition
[policy_definition]
p = sub, obj, act
# Policy effect
[policy_effect]
e = some(where (p.eft == allow))
# Matchers
[matchers]
m = r.sub == p.sub && r.obj == p.obj && r.act == p.act
An example policy for ACL model is like:
p, alice, data1, read
p, bob, data2, write
It means:
- alice can read data1
- bob can write data2
We also support multi-line mode by appending '\' in the end:
# Matchers
[matchers]
m = r.sub == p.sub && r.obj == p.obj \
&& r.act == p.actFurther more, if you are using ABAC, you can try operator in like following in Casbin golang edition (jCasbin and Node-Casbin are not supported yet):
# Matchers
[matchers]
m = r.obj == p.obj && r.act == p.act || r.obj in ('data2', 'data3')But you SHOULD make sure that the length of the array is MORE than 1, otherwise there will cause it to panic.
For more operators, you may take a look at govaluate
What Casbin does:
- enforce the policy in the classic
{subject, object, action}form or a customized form as you defined, both allow and deny authorizations are supported. - handle the storage of the access control model and its policy.
- manage the role-user mappings and role-role mappings (aka role hierarchy in RBAC).
- support built-in superuser like
rootoradministrator. A superuser can do anything without explict permissions. - multiple built-in operators to support the rule matching. For example,
keyMatchcan map a resource key/foo/barto the pattern/foo*.
What Casbin does NOT do:
- authentication (aka verify
usernameandpasswordwhen a user logs in) - manage the list of users or roles. I believe it's more convenient for the project itself to manage these entities. Users usually have their passwords, and Casbin is not designed as a password container. However, Casbin stores the user-role mapping for the RBAC scenario.
go get github.com/casbin/casbin
https://casbin.org/docs/en/overview
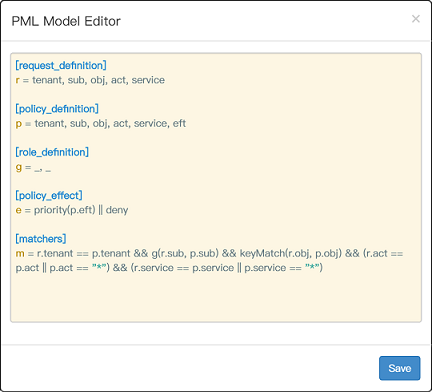
You can also use the online editor (http://casbin.org/editor/) to write your Casbin model and policy in your web browser. It provides functionality such as syntax highlighting and code completion, just like an IDE for a programming language.
https://casbin.org/docs/en/tutorials
-
New a Casbin enforcer with a model file and a policy file:
e := casbin.NewEnforcer("path/to/model.conf", "path/to/policy.csv")
Note: you can also initialize an enforcer with policy in DB instead of file, see Persistence section for details.
-
Add an enforcement hook into your code right before the access happens:
sub := "alice" // the user that wants to access a resource. obj := "data1" // the resource that is going to be accessed. act := "read" // the operation that the user performs on the resource. if e.Enforce(sub, obj, act) == true { // permit alice to read data1 } else { // deny the request, show an error }
-
Besides the static policy file, Casbin also provides API for permission management at run-time. For example, You can get all the roles assigned to a user as below:
roles := e.GetRoles("alice")
See Policy management APIs for more usage.
- Please refer to the
_test.gofiles for more usage.
Casbin provides two sets of APIs to manage permissions:
- Management API: the primitive API that provides full support for Casbin policy management. See here for examples.
- RBAC API: a more friendly API for RBAC. This API is a subset of Management API. The RBAC users could use this API to simplify the code. See here for examples.
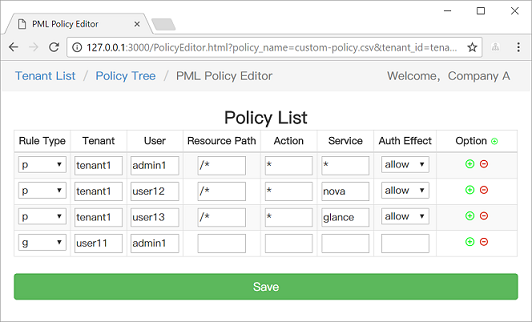
We also provide a web-based UI for model management and policy management:
https://casbin.org/docs/en/adapters
Some adapters support filtered policy management. This means that the policy loaded by Casbin is a subset of the policy in storage based on a given filter. This allows for efficient policy enforcement in large, multi-tenant environments when parsing the entire policy becomes a performance bottleneck.
To use filtered policies with a supported adapter, simply call the LoadFilteredPolicy method. The valid format for the filter parameter depends on the adapter used. To prevent accidental data loss, the SavePolicy method is disabled when a filtered policy is loaded.
For example, the following code snippet uses the built-in filtered file adapter and the RBAC model with domains. In this case, the filter limits the policy to a single domain. Any policy lines for domains other than "domain1" are omitted from the loaded policy:
import (
"github.com/casbin/casbin"
)
enforcer := casbin.NewEnforcer()
adapter := fileadapter.NewFilteredAdapter("examples/rbac_with_domains_policy.csv")
enforcer.InitWithAdapter("examples/rbac_with_domains_model.conf", adapter)
filter := &fileadapter.Filter{
P: []string{"", "domain1"},
G: []string{"", "", "domain1"},
}
enforcer.LoadFilteredPolicy(filter)
// The loaded policy now only contains the entries pertaining to "domain1".https://casbin.org/docs/en/watchers
https://casbin.org/docs/en/role-managers
If you use Casbin in a multi-threading manner, you can use the synchronized wrapper of the Casbin enforcer: https://github.com/casbin/casbin/blob/master/enforcer_synced.go.
It also supports the AutoLoad feature, which means the Casbin enforcer will automatically load the latest policy rules from DB if it has changed. Call StartAutoLoadPolicy() to start automatically loading policy periodically and call StopAutoLoadPolicy() to stop it.
The overhead of policy enforcement is benchmarked in model_b_test.go. The testbed is:
Intel(R) Core(TM) i7-6700HQ CPU @ 2.60GHz, 2601 Mhz, 4 Core(s), 8 Logical Processor(s)
The benchmarking result of go test -bench=. -benchmem is as follows (op = an Enforce() call, ms = millisecond, KB = kilo bytes):
| Test case | Size | Time overhead | Memory overhead |
|---|---|---|---|
| ACL | 2 rules (2 users) | 0.015493 ms/op | 5.649 KB |
| RBAC | 5 rules (2 users, 1 role) | 0.021738 ms/op | 7.522 KB |
| RBAC (small) | 1100 rules (1000 users, 100 roles) | 0.164309 ms/op | 80.620 KB |
| RBAC (medium) | 11000 rules (10000 users, 1000 roles) | 2.258262 ms/op | 765.152 KB |
| RBAC (large) | 110000 rules (100000 users, 10000 roles) | 23.916776 ms/op | 7.606 MB |
| RBAC with resource roles | 6 rules (2 users, 2 roles) | 0.021146 ms/op | 7.906 KB |
| RBAC with domains/tenants | 6 rules (2 users, 1 role, 2 domains) | 0.032696 ms/op | 10.755 KB |
| ABAC | 0 rule (0 user) | 0.007510 ms/op | 2.328 KB |
| RESTful | 5 rules (3 users) | 0.045398 ms/op | 91.774 KB |
| Deny-override | 6 rules (2 users, 1 role) | 0.023281 ms/op | 8.370 KB |
| Priority | 9 rules (2 users, 2 roles) | 0.016389 ms/op | 5.313 KB |
| Model | Model file | Policy file |
|---|---|---|
| ACL | basic_model.conf | basic_policy.csv |
| ACL with superuser | basic_model_with_root.conf | basic_policy.csv |
| ACL without users | basic_model_without_users.conf | basic_policy_without_users.csv |
| ACL without resources | basic_model_without_resources.conf | basic_policy_without_resources.csv |
| RBAC | rbac_model.conf | rbac_policy.csv |
| RBAC with resource roles | rbac_model_with_resource_roles.conf | rbac_policy_with_resource_roles.csv |
| RBAC with domains/tenants | rbac_model_with_domains.conf | rbac_policy_with_domains.csv |
| ABAC | abac_model.conf | N/A |
| RESTful | keymatch_model.conf | keymatch_policy.csv |
| Deny-override | rbac_model_with_deny.conf | rbac_policy_with_deny.csv |
| Priority | priority_model.conf | priority_policy.csv |
- Casbin Server: The official
Casbin as a Servicesolution based on gRPC, both Management API and RBAC API are provided. - Go-Simple-API-Gateway: A simple API gateway written by golang, supports for authentication and authorization.
- middleware-acl: RESTful access control middleware based on Casbin.
- Gin: A HTTP web framework featuring a Martini-like API with much better performance, via plugin: authz
- Beego: An open-source, high-performance web framework for Go, via built-in plugin: plugins/authz
- Caddy: Fast, cross-platform HTTP/2 web server with automatic HTTPS, via plugin: caddy-authz
- Go kit: A toolkit for microservices, via built-in plugin: plugins/authz
- Revel: A high productivity, full-stack web framework for the Go language, via plugin: auth/casbin
- Echo: High performance, minimalist Go web framework, via plugin: echo-authz (thanks to @xqbumu)
- Iris: The fastest web framework for Go in (THIS) Earth. HTTP/2 Ready-To-GO, via plugin: casbin (thanks to @hiveminded)
- Negroni: Idiomatic HTTP Middleware for Golang, via plugin: negroni-authz
- Chi: A lightweight, idiomatic and composable router for building HTTP services, via plugin: chi-authz
- Buffalo: A Go web development eco-system, designed to make your life easier, via plugin: buffalo-mw-rbac (thanks to @kgosse)
- Macaron: A high productive and modular web framework in Go, via plugin: authz
- DotWeb: Simple and easy go web micro framework, via plugin: authz
- Tango: Micro & pluggable web framework for Go, via plugin: authz
- Baa: An express Go web framework with routing, middleware, dependency injection and http context, via plugin: authz
- VMware Harbor: VMware's open source trusted cloud native registry project that stores, signs, and scans content, via direct integration, see: model (in code), policy rules (in code)
- Intel RMD: Intel's resource management daemon, via direct integration, see: model, policy rules
- VMware Dispatch: A framework for deploying and managing serverless style applications, via direct integration, see: model (in code), policy rules (in code)
- Banzai Pipeline: Banzai Cloud's RESTful API to provision or reuse managed Kubernetes clusters in the cloud, via direct integration, see: model (in code), policy rules (in code)
- Docker: The world's leading software container platform, via plugin: casbin-authz-plugin (recommended by Docker)
- Gobis: Orange's lightweight API Gateway written in go, via plugin: casbin, see model (in code), policy rules (from request)
- Skydive: An open source real-time network topology and protocols analyzer, via direct integration, see: model (in code), policy rules
- Zenpress: A CMS system written in Golang, via direct integration, see: model, policy rules (in Gorm)
- Argo CD: GitOps continuous delivery for Kubernetes, via direct integration, see: model, policy rules
- Muxi Cloud: PaaS of Muxi Cloud, an easier way to manage Kubernetes cluster, via direct integration, see: model, policy rules (in code)
- EngineerCMS: A CMS to manage knowledge for engineers, via direct integration, see: model, policy rules (in SQLite)
- Cyber Auth API: A Golang authentication API project, via direct integration, see: model, policy rules
- IRIS Community: Website for IRIS Community Activities, via direct integration, see: model, policy rules
- Metadata DB: BB archive metadata database, via direct integration, see: model, policy rules
This project is licensed under the Apache 2.0 license.
If you have any issues or feature requests, please contact us. PR is welcomed.
- https://github.com/casbin/casbin/issues
- hsluoyz@gmail.com
- Tencent QQ group: 546057381