|
| 1 | +## Diffie Hellman Key Exchange Algorithm |
| 2 | +The Diffie–Hellman (DH) Algorithm is a key-exchange protocol that enables two parties communicating over public channel to establish a mutual secret without it being |
| 3 | +transmitted over the Internet. DH enables the two to use a public key to encrypt and decrypt their conversation or data using symmetric cryptography. </br> |
| 4 | +***- https://www.hypr.com*** </br> |
| 5 | + |
| 6 | +Symmetric encryption is a type of encryption where only one key (a secret key) is used to both encrypt and decrypt electronic information. The entities communicating via |
| 7 | +symmetric encryption must exchange the key so that it can be used in the decryption process. This encryption method differs from asymmetric encryption where a pair of keys, |
| 8 | +one public and one private, is used to encrypt and decrypt messages. |
| 9 | + |
| 10 | +By using symmetric encryption algorithms, data is converted to a form that cannot be understood by anyone who does not possess the secret key to decrypt it. |
| 11 | +Once the intended recipient who possesses the key has the message, the algorithm reverses its action so that the message is returned to its original and understandable form. |
| 12 | + |
| 13 | +To understand the Math behind DH Algorithm, Kindly visit https://mathworld.wolfram.com/Diffie-HellmanProtocol.html |
| 14 | + |
| 15 | +## Libraries required for executing the algorithm : |
| 16 | +- Socket |
| 17 | +- Before working with the project, you need to keep ready ip address of your system. You can retrieve ip address by : |
| 18 | + In Command Prompt, run following command |
| 19 | + - On Windows |
| 20 | + ```ifconfig``` |
| 21 | + - On MAC / LINUX based systems |
| 22 | + ```ipconfig``` |
| 23 | + |
| 24 | +## Steps to run the program |
| 25 | +**1.** Fork [this](https://github.com/Tejas1510/Hacking-Scripts/) repository. |
| 26 | +Click on the <a href="https://github.com/Tejas1510/Hacking-Scripts/"><img src="https://img.icons8.com/ios/24/000000/code-fork.png"></a> symbol at the top right corner. |
| 27 | + |
| 28 | +**2.** Clone the forked repository. |
| 29 | + |
| 30 | +```bash |
| 31 | +git clone https://github.com/<your-github-username>/Hacking-Scripts |
| 32 | +``` |
| 33 | +**3.** Navigate to the project directory. |
| 34 | + |
| 35 | +```bash |
| 36 | +cd Hacking-Scripts/python/RSA Algorithm |
| 37 | +``` |
| 38 | +**4.** Run the python file. |
| 39 | +- First run alice.py |
| 40 | +```bash |
| 41 | +python alice.py |
| 42 | +``` |
| 43 | +- Then run bob.py |
| 44 | +```bash |
| 45 | +python bob.py |
| 46 | +``` |
| 47 | +# Demonstration of Exchange : |
| 48 | +## Output of Alice(Sender) file : |
| 49 | + -You need to enter ip address of your system at underlined part : |
| 50 | + 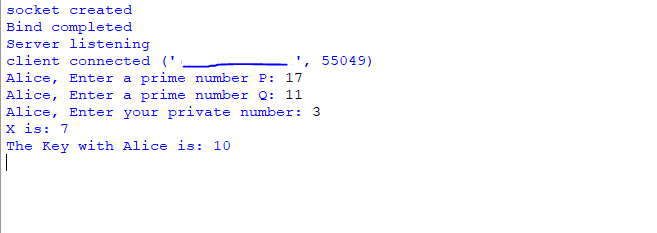 |
| 51 | + |
| 52 | +## Output of Bob(Receiver) file : |
| 53 | +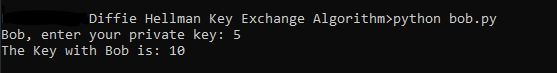 |
| 54 | + |
| 55 | +## Conclusion: |
| 56 | +As you can see how the secret key is established between sender and receiver without it being transmitted over the Internet to communicate with each other. |
| 57 | + |
| 58 | +### References |
| 59 | +- https://www.cryptomathic.com/news-events/blog/symmetric-key-encryption-why-where-and-how-its-used-in-banking |
| 60 | + |
| 61 | + |
| 62 | +### Contributed by : [@NikitaEmberi](https://github.com/NikitaEmberi) |
0 commit comments